The Presidential Records Act (PRA) was enacted to ensure that all presidential communications and records are preserved, thereby promoting transparency and accountability within the executive branch. The PRA mandates that the official actions and communications of the President or Vice President and his immediate staff be documented and maintained as part of the historical record, reflecting the President’s constitutional and statutory duties (44 USC § 2203). This legal framework distinguishes between official acts—those conducted in the capacity of executing presidential responsibilities—and unofficial acts, which are personal or political and fall outside the scope of these responsibilities (Nixon v. Fitzgerald, 457 US 731 (1982)).
Transparency and accountability are foundational principles in a democratic society, ensuring that governmental actions are open to scrutiny and oversight (Federalist No. 70, Alexander Hamilton). By preserving official records, the PRA enables the public, historians, and legal authorities to evaluate presidential actions, thus safeguarding the integrity of the office and promoting trust in the government (44 USC § 2203(f)). When communications are conducted through private channels and not preserved as required by the PRA, it undermines these principles, suggesting an intent to evade accountability (Clinton v. Jones, 520 US 681 (1997)). Such actions raise significant concerns, mainly when they involve non-official entities and are routed through foreign servers to avoid detection by national security agencies. These factors strongly indicate that the actions in question are unofficial and should be treated as such to uphold the standards of transparency and accountability mandated by the PRA (United States v. Nixon, 418 US 683 (1974)).
Violation of the PRA Indicates Intent to Evade Official Accountability And Therefore All Actions Should Be Considered Unofficial
The PRA aims to ensure that all official actions are documented and preserved. It mandates that any official communication or action undertaken by the President must be recorded and maintained to allow for future scrutiny and historical record (44 USC § 2203). This ensures that the President’s actions are transparent and accountable to the public, Congress, and historians.
Routing communications through private emails and foreign servers indicates a deliberate attempt to avoid this requirement. When presidential communications are conducted outside official channels and not preserved as the PRA requires, it suggests a conscious effort to circumvent the law’s intent. This is particularly concerning when these communications are routed through private emails and foreign servers, which are inherently less secure and less subject to US governmental oversight. Such actions raise significant red flags about the motives behind these communications.
RELATED: EVIDENCE| Secret Emails Used By Obama and Biden Are Hosted By German Intelligence – Tore Says
The deliberate use of private channels to conduct official business undermines the PRA’s foundation. This act of circumventing official channels violates the law’s letter and spirit, rooted in transparency and accountability. Intentionally avoiding official documentation suggests an intent to evade scrutiny and prevent responsibility for potentially controversial or unlawful activities (Clinton v. Jones, 520 US 681 (1997)).

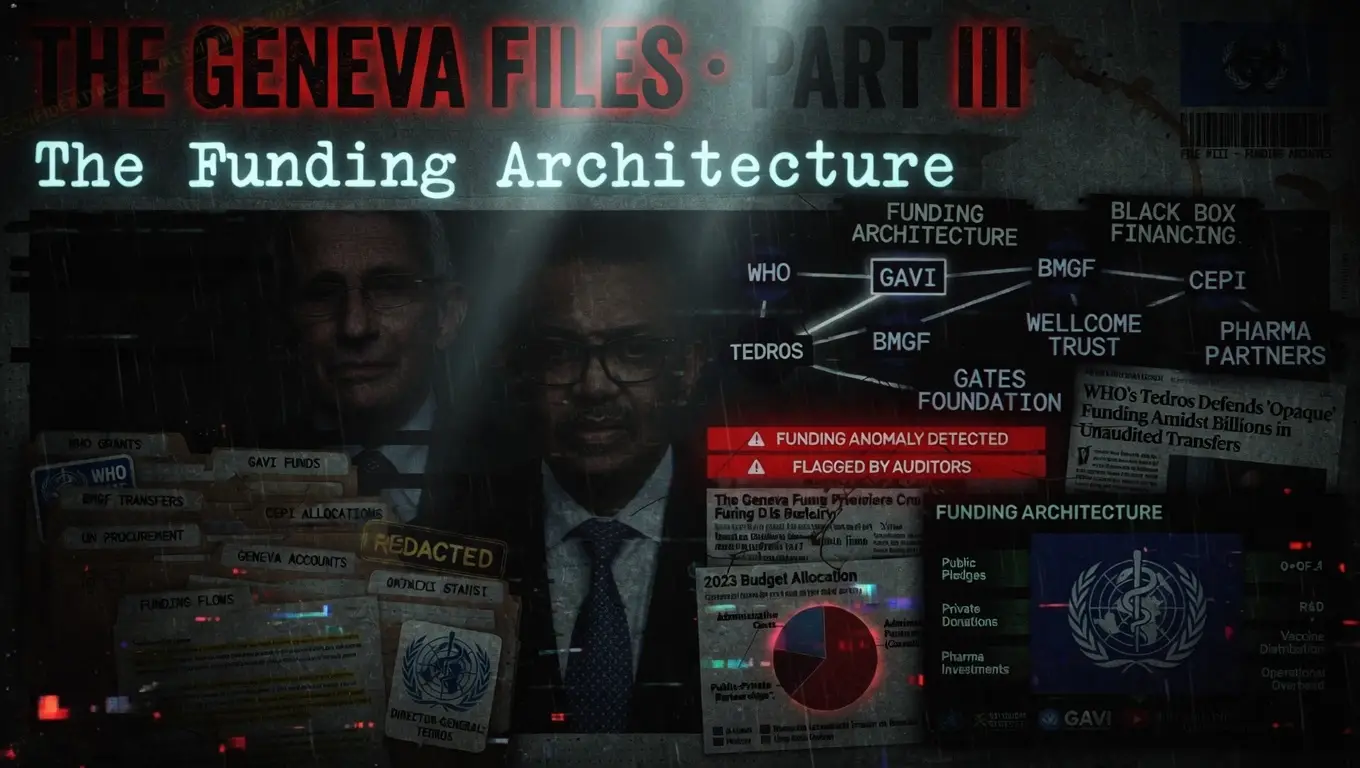
Furthermore, routing communications through foreign servers to evade detection by the NSA and other national security agencies exacerbates the issue. Such actions indicate not just an intent to avoid public accountability but also an effort to conceal communications from domestic security and intelligence oversight. This poses significant risks to national security and undermines the integrity of the presidential office. Foreign servers could expose sensitive information to adversaries, highlighting these communications’ unofficial and potentially illicit nature.
It is essential to get a bit of background to things that occurred. Hence, you, the reader, understand the importance of the information being provided and how today’s SCOTUS decision on Presidential Immunity draws the line between official and unofficial duties. This article has been in the making with over a decade’s work and sheds light on a well-coordinated effort among agencies loyal to “The Plan” to abuse their position of power. This is a robust assertion, but by the end of this article, you will understand why this assertion is valid.
Jeh Johnson’s Unprecedented Declaration on January 6, 2017
The DHS was established in 2002 in response to the 9/11 terrorist attacks, with a mission to safeguard the United States against a wide range of threats, including cybersecurity. Within DHS, the Cybersecurity and Infrastructure Security Agency (CISA) was created to oversee the cybersecurity of federal civilian executive branch networks and critical infrastructure.
While DHS and CISA now play significant roles in the broader context of federal cybersecurity, including protecting critical infrastructure and ensuring secure communications across government networks, the direct oversight of presidential communications, particularly those of a highly sensitive or classified nature, remains primarily with agencies like the NSA and WHCA (U.S. Department of Homeland Security) (U.S. Department of Homeland Security) (U.S. Department of Homeland Security)
The announcement by then-Secretary of Homeland Security Jeh Johnson on January 6, 2017, to designate U.S. election infrastructure as a critical infrastructure subsector was significant, particularly during the presidential transition period. It is unprecedented for such declarations and substantial changes to government operations and positions to occur during the Presidential Transition Period, including the fact that Barack Obama made the IG of the NSA a presidential appointment. Vital decisions to be made during this time should be scrutinized due to the sensitive nature of the transition of power, which heavily indicates the undermining of the upcoming presidential administration.
On January 6, 2017, then-Secretary of Homeland Security Jeh Johnson announced the designation of U.S. election infrastructure as a subsector of the nation’s critical infrastructure. This decision was based on elections’ vital role in the democratic process and the need to protect them from increasing cyber threats. The designation means that election infrastructure, including storage facilities, polling places, vote tabulation locations, voter registration databases, and voting machines, would receive prioritized cybersecurity assistance from the Department of Homeland Security (DHS) through the Cybersecurity and Infrastructure Security Agency (CISA) (U.S. Department of Homeland Security) (Intelligence Community News).
Furthermore, the Protected Critical Infrastructure Information (PCII) Program, managed by the Cybersecurity and Infrastructure Security Agency (CISA) within the Department of Homeland Security (DHS), is designed to enhance information sharing between the private sector and the government. Ministry of Truth, anyone? This program offers legal protections for sensitive information about critical infrastructure voluntarily shared with the government, ensuring that such information is not publicly disclosed and is used solely for homeland security purposes.
Purpose and Function
The primary goal of the PCII Program is to protect critical infrastructure information from public disclosure under the Freedom of Information Act (FOIA) and other state and local disclosure laws. This protection encourages private entities to share information about vulnerabilities and threats without fear of public exposure or misuse in regulatory actions and civil litigation. This information is vital for the government to analyze and secure critical infrastructure, identify vulnerabilities, and develop risk assessments and mitigation strategies (CISA) (CISA).
Predecessor to PCII is PCI
Before the creation of CISA, it was asserted that domains such as pci.gov existed as precursors to the formal establishment of the PCII Program. These would have been aimed at managing and protecting critical infrastructure information. The PCII Program, as it stands today, formalizes these efforts under a regulated framework, ensuring that the information shared between the private sector and the government is safeguarded and used appropriately to bolster national security (CISA) (CISA).
Now that we have a better understanding of the PCI.gov cloaked emails managed by DHS that were used during the tenure of President Obama and then Vice President Biden, it still does not offer clarity on why they used GERMAN INTELLIGENCE SERVERS for communications. This further reinforces the notion that the communications conducted under the purview of DHS and those via German Intelligence are being co-mingled when they are two separate issues to obfuscate two inappropriate, unethical, and illegal acts conducted by the Obama administration. This has happened before.
The Dismissal of Dennis Blair And The False Narrative That Followed
During Barack Obama’s administration, John Owen Brennan, who served as the Deputy National Security Advisor for Homeland Security and Counterterrorism, was involved in various covert operations. Brennan, a former CIA officer, played a crucial role in shaping counterterrorism policies. He was initially tapped to lead the CIA but withdrew due to opposition related to his past support of controversial interrogation tactics. Instead, he served as a critical advisor to President Obama, where he was involved in counterterrorism initiatives that expanded upon the strategies of previous administrations, including those under George W. Bush (Wikipedia) (IISS).
Brennan’s tenure involved the creation of agencies and sub-agencies without formal charters, ostensibly for anti-terrorism purposes. These entities sometimes operated in a legal gray area, engaging in surveillance activities within the United States (CONUS) and abroad (OCONUS). These operations aimed to gather intelligence on individuals with information about ambiguous activities funded by U.S. taxpayer dollars (PolitiFact).
A notable incident occurred when Dennis Blair, then Director of National Intelligence, inadvertently mentioned these operations in an interview, namely the High-Value Intelligence Group, which I was part of, which led to his dismissal. The Obama administration quickly rebranded the project to align with the official narrative, attempting to maintain control over the dissemination of information and the scope of these covert activities.
John Brennan oversaw the capture of Senate and Congressional communications networks and stored sensitive critical management systems (CKMS) data in Germany. These actions reflect broader concerns about government overreach and the balance between national security and civil liberties (Wikipedia) (IISS). This was intentional as I was part of HVIG and then coined HIG, which became a PROJECT ENTITY NAME that is still classified today.
In other words, DHS having an agency “off books” like PCI (Presidential Communications Infrastructure) is the same as that of HVIG (High-Value Intelligence Group), which existed without charter, oversight and operated on SES funds and or allocated funds such as the State Department’s INL and other obscure programs that at the core are highly compartmentalized and or “non-existent” on paper.
Is it starting to make sense as to why the former ODNI James Clapper and former CIA Director John Brennan, along with other Intelligence Officials, LIED about Hunter’s laptop? Because it implicates many agencies and officials and, in turn, destroys ANY credibility of the US government, which is a vast national security risk. Even though they lied, the lie has been FORCED on them for National Security reasons even though it is WRONG. #SpyFall
Given the context of the PCI.GOV explanation provided by US Officials and their conduits, it becomes clear how crucial the choice of words and underlying intentions are. As James Comey highlighted, “intent” is critical in determining criminal activity, demonstrated by multiple factors, not just a single instance. Let’s examine that.
Involvement of Non-Official Entities such as Hunter Biden and others.
Based on the pertinent, up-to-date information, it is essential to note that the involvement of non-official entities in such communications further supports their unofficial nature. (multiple factors to prove intent). Official communications typically involve interactions with government officials and agencies to ensure adherence to established protocols and accountability standards. When private individuals or foreign actors not engaged in diplomatic roles are part of these communications, the exchanges serve personal or political purposes rather than official presidential duties. This deviation from the standard protocol raises concerns about the intent behind such communications and suggests an effort to circumvent transparency and accountability requirements, thus reinforcing their unofficial status (CISA) (CISA).

The involvement of non-official entities in these communications further supports such communications’ unofficial nature. Official communications, as mandated by the Presidential Records Act (PRA), should involve interactions with government officials and agencies directly related to executing presidential and or vice presidential duties. When communications extend to private individuals or foreign actors in a non-diplomatic capacity, they fall outside official presidential responsibilities. This deviation from standard protocol indicates that the communications in question are not part of the President’s official duties but serve personal or political interests.
Official Acts vs Non-Official Acts
The distinction between official and unofficial acts is critical in evaluating executive office communications, especially when considering the involvement of non-official individuals, such as the president’s family members, in sensitive communications with foreign leaders. This distinction, as established in Nixon v. Fitzgerald, 457 U.S. 731 (1982), provides that a sitting President or Vice President is entitled to absolute immunity from civil damages for actions taken within the “outer perimeter” of his official responsibilities, which includes constitutional and statutory duties. In contrast, unofficial acts, which are personal or political, do not enjoy such protections (Justia). The United States Supreme Court reinforced that today with their 6-3 ruling on Presidential Immunity.
In the context of Hunter Biden, who had no official role in his father’s administration, his communications with foreign leaders determine their nature. Since Hunter Biden was not a government official, his involvement in such communications could not be part of any official duty. Official presidential communications typically involve policy discussions, diplomatic negotiations, and national security matters conducted by designated officials (Nixon v. Fitzgerald). Hence, the media and Obama-Biden camp complaining of Jared Kushner’s involvement in such communications have NO MERIT because Jared Kushner had an OFFICIAL role in the Trump Administration.
These communications were related to Hunter Biden’s business interests or political activities and were classified as unofficial acts. If his presence on the call was to help his private business dealings, then such communications are classified as unofficial acts. For example, if Hunter Biden discussed business opportunities or leveraged his relationship with his father for personal gain, these actions would fall outside the scope of protected official actions.
The Eastern District of New York Prosecution of Andrii Derkach
Andrii Derkach, a Ukrainian politician who lied about the laptop, also stated he was a Russian agent, and they indicted him for violating U.S. sanctions. His actions were part of a broader falsy purported by the same 51 spies who lied, an alleged disinformation campaign to influence the 2020 U.S. Presidential election. It’s good that John Durham is watching Breon’s fantastic “cleaning” techniques for the Obama administration. It’s pretty genius but highly apparent.
The call referenced earlier in this report, the email to which Hunter Biden was invited to sit in on and briefed on by the Executive Office is one of the calls Andrii Derkach released the audio of. Then Vice President Biden conversing with President Poroshenko throughout the month of 2016 to which Hunter Biden was also involved in at least one of these phonecalls. The lawfare and target on Derkach as a whistleblower for the Ukrainian governement has deterred any further commentary. As someone who has spent time working on projects in Ukraine specifically between 2012-2014 prior to my erasure from all records and having one of the Hunter Biden laptops and parts of the others I can piece this together for you.
RELATED: Biden audio first shared by ‘Russian agent’ thrives online | AP News
The media and the US Government employed one of the FOUNDERS of Disinformation Intitiatives that ORIGINATED in Ukraine: Nina Jankowicz
“It’s certainly an influence campaign,” Nina Jankowicz, a disinformation fellow at the nonpartisan Wilson Center, said of the recordings. “It’s misleading to an audience that doesn’t have the full picture.”
Biden audio first shared by ‘Russian agent’ thrives online | AP News
In all fairness she is right because there are THREE distinct recording of THREE distinct convesations that were postured by the media in the “leak” as ONE phonecall. Which regardless, demonstrates without any question that the US Government blackmailed the Ukraine to appoint their choice of prosecutor in oreder to obtain the monies they required to deter governmental collapse. It is important to again note that at least three phone calls are in that audio and I analyze that for you in the video I will be releasing tonight at 1900 EST on X and Rumble. Has anyone FOIAd these communications? Probably not but a prosecutore observing “clear as day” blackmail of our government upon another may have those communications. In fact, Derkach phone call leaks are so accurate that he is still being persecuted by the Biden Administration for various allegations to silence, jail and exterminate the threat he poses to the legacy of the Obama regime and his alleged administartion. Almost like Biden has weaponized the DOJ to hinder whistleblowers and those that challenge his unofficial acts with the power of the Executive office between 2009-2016 and 2020 until today.
Biden’s DOJ is going after Derkach for conducting obscure shell company business activites that are part in parcel in Ukraine. Even Joe Biden’s son on the record said “shennanigans” refering to shell companies are almost necessary to operate effectively in Ukraine.
We can not kid ourselves into thinking that any successful business in Ukraine in the past 20 years was created without some shenanigans that we in the US would find questionable at best. I really want you guys to push them to radically alter the way they are thinking about how they will do business going forward.
Hunter Biden in above email
Transparency and accountability are foundational principles in a democratic republic. As articulated by Alexander Hamilton in Federalist No. 70, these principles are crucial for ensuring that public officials, including the President, Vice President and immediate staff of the President (like Karl Rove, Ron Klain or John Flynn), act in the best interests of the nation. Transparency allows the public to see and understand the actions of their leaders, fostering trust and confidence in government institutions. Accountability ensures that public officials can be held responsible for their actions, deterring misconduct and promoting ethical governance.
The preservation of records is a critical aspect of maintaining transparency and accountability. The Presidential Records Act (PRA), codified at 44 U.S.C. § 2203(f), mandates the preservation of official records created or received by the President or his immediate staff. This law ensures that the actions and decisions of the President, Vice President and immediate staff of the President are documented, enabling the public, historians, and legal authorities to evaluate presidential actions accurately. By maintaining comprehensive records, the PRA helps protect the integrity of the executive branch and provides a vital check on presidential power.
However, evasion of accountability occurs when communications are conducted through private channels and not preserved as required by the PRA. This undermines the principles of transparency and accountability. The Supreme Court’s decision in Clinton v. Jones (520 U.S. 681, 1997) highlights the importance of maintaining official records. In this Supreme Court Case, the Supreme Court emphasized that private actions by a President are not shielded by absolute immunity, underscoring the necessity for transparency and accountability even at the highest levels of government. By circumventing official communication channels, a President, Vice President and immediate staff of the President can evade scrutiny and accountability, which erodes public trust and the democratic process.
Consider the implications of the Hunter Biden laptop controversy, where private emails revealed discussions that would be considered presidential communications. Such incidents demonstrate the dangers of bypassing official communication channels and the potential for significant breaches in accountability and transparency. When leaders conduct official business through private means, they not only violate legal mandates but also betray the public’s trust.
Now, we have the Supreme Court providing us with the necessary tools to investigate illicit misconduct. Armed with the Supreme Court’s decision in Clinton v. Jones (520 U.S. 681, 1997), we understand the critical importance of maintaining official records. This landmark case emphasized that private actions by a President are not shielded by absolute immunity, reinforcing the necessity for transparency and accountability even at the highest levels of government.
Furthermore, the recent Supreme Court ruling in Donald Trump v. United States has defined the distinction between official acts and unofficial acts of a President, Vice President and immediate staff of the President. This decision underscores that while a President is entitled to immunity for official actions within the outer perimeter of their responsibilities, there is no such immunity for unofficial acts. This clarity is crucial for investigating and holding Presidents and their administrations, either current or former, accountable for any misconduct committed under the guise of their office.
These judicial decisions collectively strengthen our legal framework, ensuring that no President is above the law. They mandate the preservation of official records as outlined by the Presidential Records Act (PRA), codified at 44 U.S.C. § 2203(f), which is essential for maintaining transparency and accountability. The PRA ensures that the actions and decisions of the President, Vice President and immediate staff of the President are documented, enabling the public, historians, and legal authorities to accurately evaluate presidential actions.
The evasion of these responsibilities by using private communication channels, as illustrated in the Hunter Biden laptop, highlights the risks of undermining transparency and accountability. Such actions not only violate legal mandates but also erode public trust.
In conclusion, with the Supreme Court’s rulings in Clinton v. Jones and Donald Trump v. United States, we are better equipped to distinguish between official and unofficial acts of a President, Vice President and immediate staff of the President and ensure that all actions are subject to scrutiny.
The cover up is worse that the lie and remember, Be Careful What You Wish For.
Special thanks to : Jack Smith (or whatever his name really is)
Like my work, you can tip me or support me via TIP ME or support me on Subscribestar! I am 100% people-funded.









Brendaburgher
Now we know why Obama was able to keep his BlackBerry.
https://www.nbcnews.com/id/wbna28780205